On April 24th, CrowdStrike CEO George Kurtz appeared on TBPN and said something that every security leader, data leader, and frankly every hiring manager in tech should hear. North Korean threat actors from a group called Silent Chollima have been posing as American employees, getting hired at U.S. companies, and then having their work laptops physically shipped to mule locations inside the country. From there, the laptops get forwarded to overseas laptop farms where North Korean operators take remote control.
Kurtz put it simply:
"The laptop that you send them gets sent somewhere in the US to a mule, and that mule takes it to a laptop farm. Then the North Koreans control it and bypass all of your security because you just handed them a laptop."
And then the detail that floored me. When one company was told the person they hired was actually a North Korean operative, they went to the hiring manager. His response? "They do really good work. Can we keep them?"
I laughed, and then I felt a little sick. Because the real punchline is not that someone almost kept a North Korean spy on payroll. The real punchline is that most companies have already handed adversaries something more dangerous than a laptop. They have handed them the data on it.
This Is Not a New Kind of Attack. It Is an Old Kind of Vulnerability.
CrowdStrike has been tracking this. Famous Chollima, their name for the North Korean insider threat group, has seen a 220% year-over-year increase in activity. They investigated more than 320 incidents in a single 12-month period. These operatives use deepfake video in interviews, AI-generated resumes, and real-time English fluency tools to pass hiring screens. Once inside, they use remote monitoring tools to maintain persistence and exfiltrate data.
But here is the part the security industry keeps dancing around: the laptop farm scheme works because of what lives on the laptop.
Think about a typical data analyst, finance team member, or ops professional at a mid-market or enterprise company. On any given week they might:
- Export a 500,000 row dataset from Snowflake or Redshift into a CSV
- Open it in Excel, do some analysis, save the file locally
- Email it to a colleague or drop it in a shared folder
- Build a financial model on their machine that references live numbers from a data warehouse
- Download a customer list to do some segmentation in Google Sheets
Every one of those actions creates a local file. A static snapshot of sensitive data sitting on an endpoint that your security team cannot govern, cannot revoke, and cannot track once it leaves your cloud environment.
Now give that laptop to a North Korean threat actor. Or a disgruntled insider. Or a careless employee whose machine gets stolen at a coffee shop. The data is already there. The breach already happened the moment that CSV landed on the hard drive.
The Spreadsheet Is the Attack Surface Nobody Talks About
When most people think about data security, they think about perimeter security, identity management, zero trust architecture. Those things matter enormously. But there is a massive, largely unaddressed gap in how enterprises think about security at the last mile of data analysis.
Your data warehouse is locked down. Your cloud environment is audited. Your SaaS tools require SSO and MFA. And then your analysts export everything into Excel and go to work.
That export is where governance ends. The moment data leaves the warehouse and lands in a local file, it is outside your security perimeter. It is on the device. And as Kurtz just reminded us, the device can end up anywhere.
This is not hypothetical. Some of the largest data breaches in recent years have involved spreadsheet files on laptops or in email attachments, not compromised cloud infrastructure. The cloud part was fine. The laptop part was the problem.
What We Built at Row Zero, and Why Security Drove Every Decision
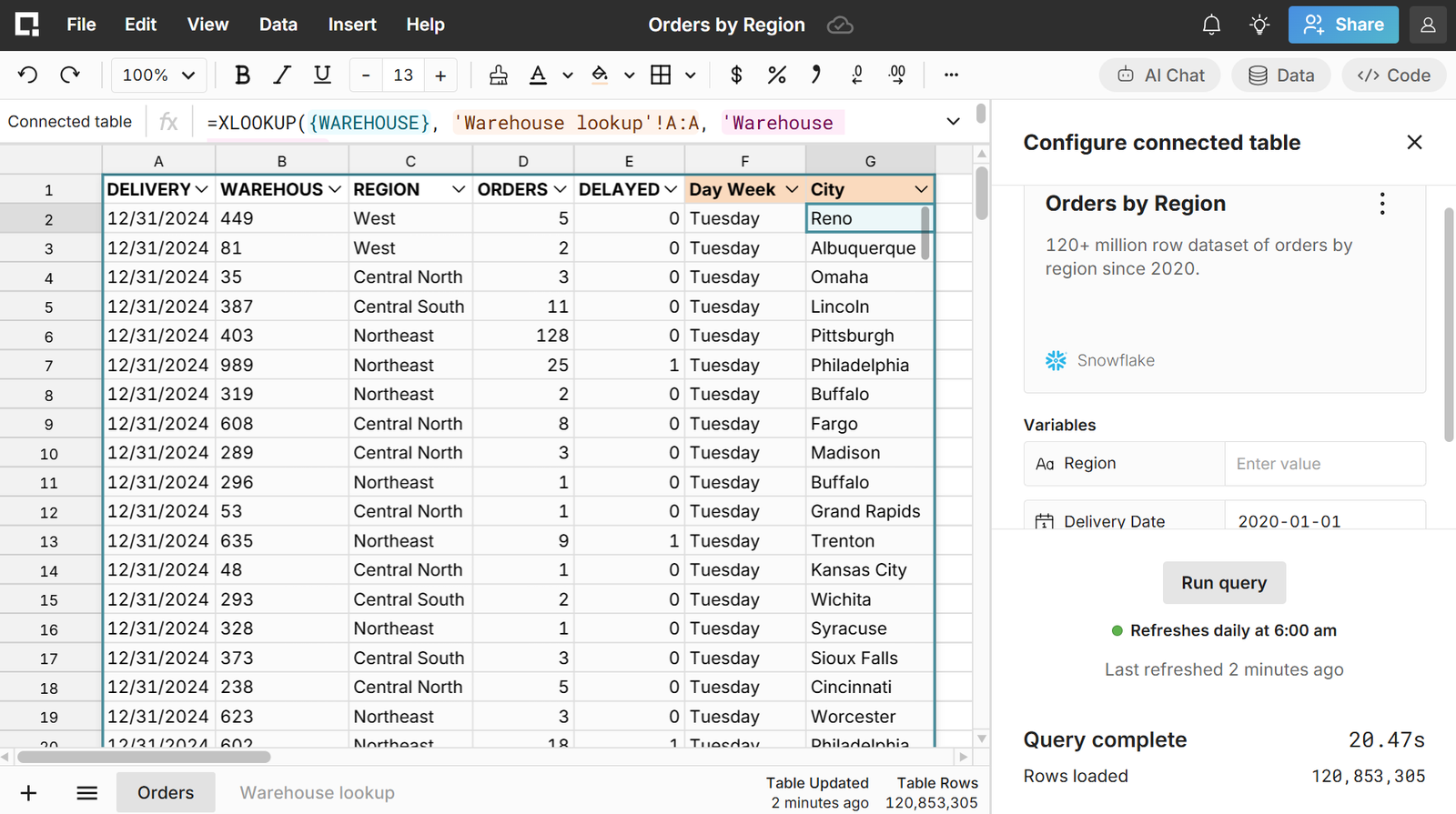
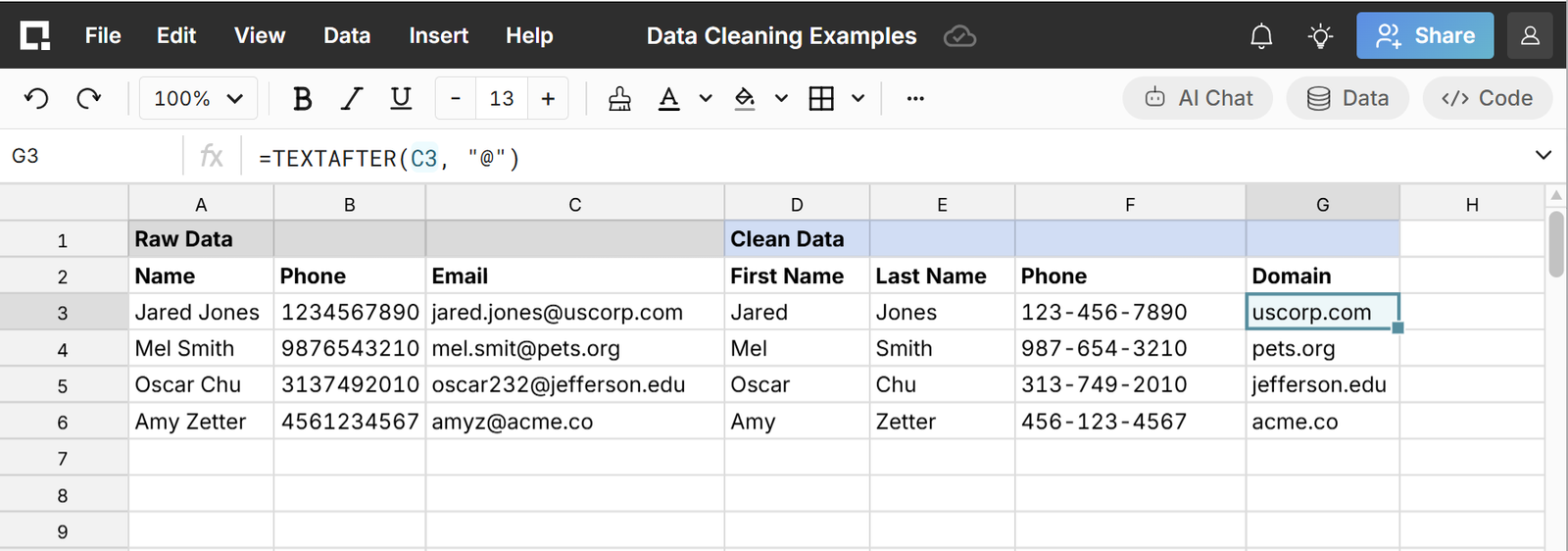
Row Zero is a cloud spreadsheet built for modern enterprise data. We scale to 2 billion rows, connect live to data warehouses like Snowflake, Databricks, Redshift, BigQuery, Postgres, S3, and Oracle, and give teams the familiar Excel and Google Sheets experience they already know. But when we designed the platform, we made a deliberate architectural choice that I want to be very explicit about:
Data never has to leave the cloud. No local files. No CSV exports to laptops. No static snapshots sitting on endpoints.
That is not a marketing line. It is a fundamental design decision that closes the attack surface that the Silent Chollima laptop farm scheme exploits.
Here is what that looks like in practice:
No Data on the Endpoint
When an analyst opens Row Zero and connects to their data warehouse, they are working with live data in a governed cloud environment. The data does not download to their machine. It does not create a local file. If their laptop gets stolen, shipped to a mule, or handed to a threat actor, there is no spreadsheet file on it with your customer data, financial projections, or operational metrics.
You gave them the laptop. You did not give them the data.
Export Controls and Clipboard Limits
Row Zero gives administrators granular control over what users can do with data inside a spreadsheet. That includes:
- Disabling data exports entirely for specific datasets or user groups
- Restricting clipboard access so data cannot be copied out and pasted into other applications
- Preventing file downloads so sensitive analyses stay in the cloud
- Setting row-level security so users only see the data they are authorized to see, even within a shared spreadsheet
This matters because even if a threat actor has remote access to a machine, the controls live in Row Zero's cloud infrastructure, not on the device. You cannot bypass a cloud-enforced export restriction by controlling the endpoint.
Private Link and Network Isolation
Row Zero supports Private Link for data warehouse connections, meaning the connection between Row Zero and your Snowflake, Redshift, or BigQuery environment never traverses the public internet. For organizations with strict data residency or network isolation requirements, this is essential. The data pipeline is private, encrypted, and audited end to end.
Zero Data Retention (ZDR)
Row Zero operates under a Zero Data Retention policy, which means that when your data is processed, it is not stored, logged, or saved on our end after the session is complete. No retention means no exposure. There is no server-side copy of your billion-row dataset sitting in a log file somewhere waiting to be breached, subpoenaed, or accidentally leaked. For organizations operating under GDPR, CCPA, or internal data minimization mandates, ZDR is not a nice-to-have, it is the standard. In a threat environment where the CrowdStrike CEO is describing nation-state actors gaining physical access to company hardware, the last thing you want is your most sensitive data persisted anywhere it does not need to be. With Row Zero, it is not.
Role-Based Access Control and Row-Level Security
Not every analyst should see every row. Row Zero enforces role-based access control and row-level security at the platform level, so a finance analyst in EMEA sees EMEA revenue data, not global revenue data. A sales rep sees their book of business, not the entire customer list. These are not permissions that live in a local file. They are enforced in the cloud on every query, every session, every time.
If someone with unauthorized access somehow gets into a Row Zero session, they still only see what they are permitted to see. The governance travels with the data, not with the device.
SSO, SCIM, and OAuth
Row Zero integrates with enterprise identity providers via SSO and supports SCIM for automated user provisioning and deprovisioning. The moment an employee is offboarded, their Row Zero access is revoked. Instantly. They do not have a folder full of Excel files on their laptop that they took with them. The connection to the data is severed the moment the identity is.
OAuth is supported for data warehouse authentication, meaning Row Zero can connect to your data sources using your existing identity infrastructure without requiring separate credentials to be managed or stored.
SOC 2 Type II, HIPAA, and GDPR
Row Zero is SOC 2 Type II certified and compliant with HIPAA and GDPR. These are not checkbox certifications. They represent ongoing third-party audits of our security controls, data handling practices, and incident response processes. For enterprise customers with regulatory obligations around data handling, this is the baseline expectation. We meet it.
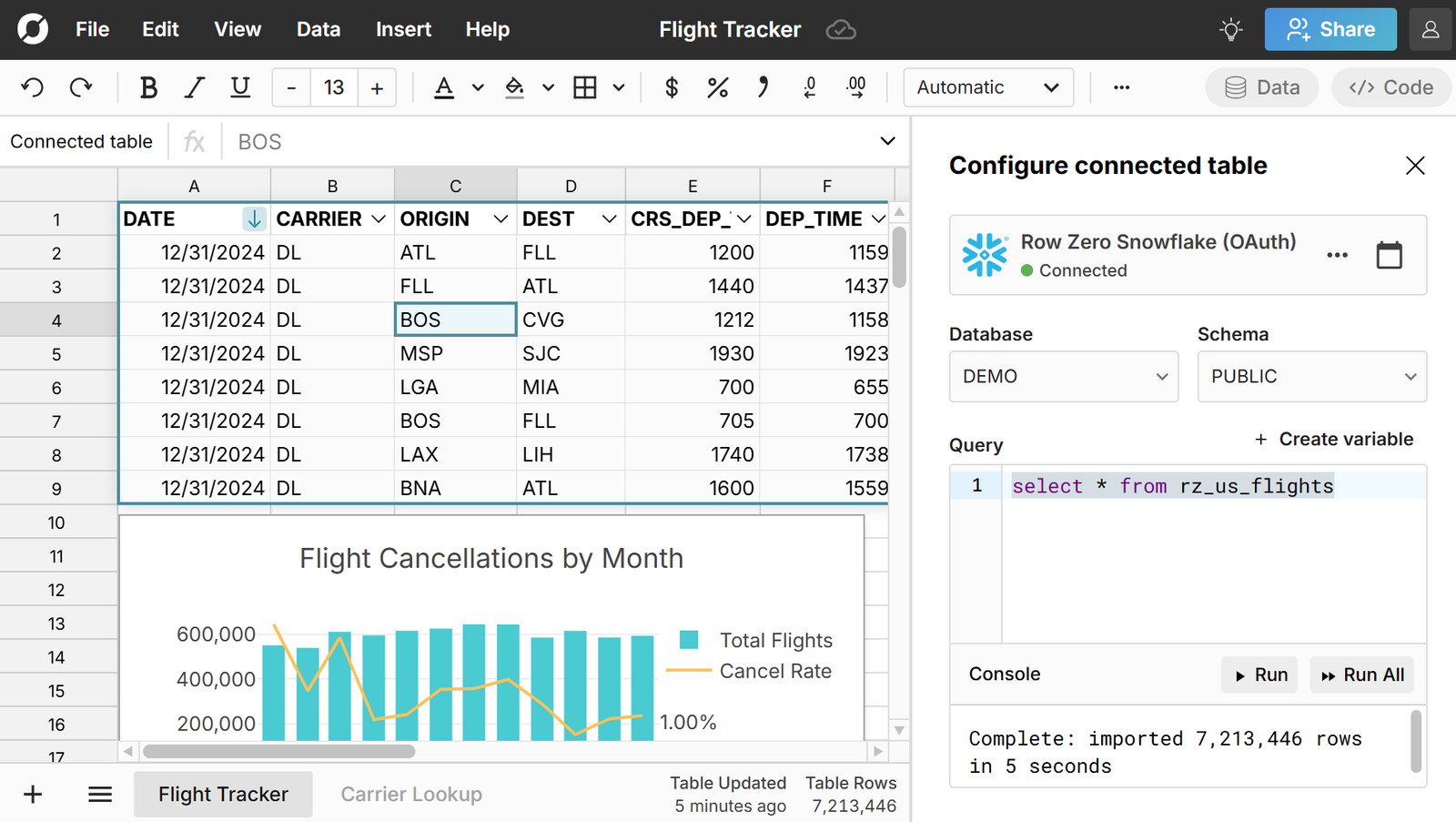
The AWS Example Hits Different Now
We published a case study about how AWS rolled out Row Zero across their teams. The context was performance and self-serve analytics. But reading it through a security lens after watching the Kurtz interview, one paragraph stands out:
"Instead of exporting sensitive datasets into static files, Row Zero connects to Amazon S3, Amazon Redshift, Amazon RDS, Amazon Athena and other data repositories so teams can work in a spreadsheet while data stays within a governed cloud environment."
That is the thing. AWS evaluated 13 different solutions before selecting Row Zero. One of their core requirements was keeping governed data in the cloud. They did not want static files on user devices. They wanted the spreadsheet experience without the endpoint risk.
The result? Teams that used to spend hours updating spreadsheets that would then sit on local machines are now doing that same analysis in seconds, with the data never leaving their governed cloud environment. Six to seven hours saved per day, per team. And zero local spreadsheet files with sensitive data sitting on company laptops.
If a North Korean threat actor got remote access to an AWS analyst's laptop tomorrow, they would find Row Zero open in a browser. They would not find a CSV with 50 million rows of customer transaction data. Because that data never left Redshift.
The Uncomfortable Conversation the Industry Needs to Have
I want to be direct about something. The security industry has done an exceptional job hardening cloud infrastructure over the past decade. Zero trust architecture, identity-based perimeters, encrypted data pipelines, continuous monitoring. The cloud is genuinely more secure than it used to be.
But we have collectively done a poor job at the last mile. The moment business users need to do analysis, the default behavior is still: export the data, open it locally, work in Excel. That behavior is a structural security gap, and no amount of EDR software, firewall rules, or zero trust policy closes it. Because the data left the perimeter the moment someone clicked Export.
The Silent Chollima threat is vivid and dramatic because it involves nation-state actors and laptop farms. But the underlying vulnerability is one that thousands of companies have every single day, with no North Koreans required. Disgruntled employees. Phished credentials. Stolen devices. Shared Excel files sent to the wrong address. Every one of those scenarios is made dramatically worse by the fact that sensitive data lives on endpoints.
The fix is not complicated. Stop putting data on devices. Work with it in the cloud, in a governed environment, with controls that travel with the data rather than with the machine.
That is what Row Zero does. It is why we built it this way. And it is why, if you watched the Kurtz interview and felt even a flicker of recognition about your own organization, it is worth taking a look.
Keep your data in the cloud where it belongs.
Try Row Zero free or request a security-focused demo at rowzero.com